Valhalla#
README
Valhalla#
The Valhalla analyzer queries the Valhalla YARA rule databased and retrieves the matching YARA rules.
Requirements#
Scope#
The result contains all matching YARA rules including
- Nextron's rules in the public rule repository
- Nextron's rules sold in the form of the YARA rule feed
The result does not contain matches with YARA rules
- submitted by 3rd parties into the public rule repository due to legal restrictions
- rules that are tagged as confidential and can therefore only be used in Nextron's scanner THOR
- rules that require external variables and can therefore only be used in Nextron's scanner THOR
The database contains YARA rule matches on samples submitted to Virustotal and Nextron's internal sample matching, which accounts for less than 1% of the matches within that database. The database does not contain information on samples that have not been transmitted to Virustotal.
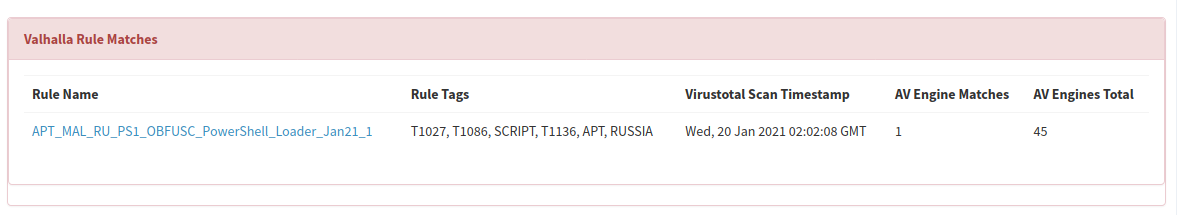
Matches#
The matches in the long report link to rule info pages that contain more information, like other matching samples, a report or public source in which the sample from which that rule was derived has been mentioned.
They also include the Antivirus detection rate at the moment of the first submission to Virustotal, which gives a good indication of the overall coverage.
Valhalla_GetRuleMatches#
Author: Florian Roth
License: AGPL-V3
Version: 0.3.1
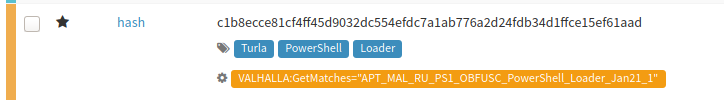
Supported observables types:
- hash
Registration required: False
Subscription required: False
Free subscription: False
Third party service: https://valhalla.nextron-systems.com
Description#
Gets matching YARA rules for a given sample SHA256 hash
Configuration#
| key | API key for Valhalla |
|---|---|
| Default value if not configured | 1111111111111111111111111111111111111111111111111111111111111111 |
| Type of the configuration item | string |
| The configuration item can contain multiple values | False |
| Is required | True |
Templates samples for TheHive#